Iran's Blocking their Backbone, WWW
time they would have to filter the WWW.
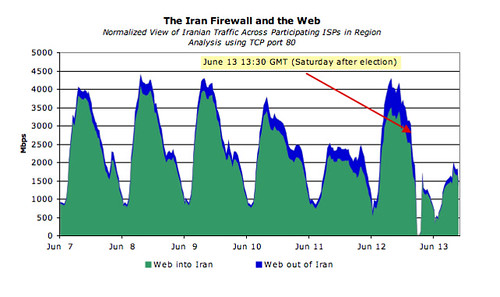
They cut out going traffic to zero, and slowly applied filters and
brought it back up.
The speed and depth of the operation indicates it was expected
they would need to shut off parts of the WEB. G

Thanks to the cooperation of several ISPs in the region and Internet Observatory data, we can now do a bit better than speculate — we have pieced together a rough picture of what the Iranian government’s Internet firewall appears to be doing. The data shows that DCI, the Iranian state run telecommunications agency, has selectively blocked or rate-limited targeted Internet applications (either by payload inspection or ports).
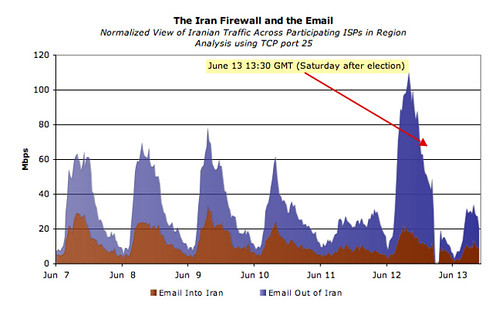
The next graph on Iranian applications filters shows email into and out of the country. Again note the run up in email traffic immediately preceding the election (especially outbound mails). And then? The data suggests DCI began blocking some outgoing email even before the election completed. Following the election, email returned at reduced levels (again, presumably because DCI had filtering infrastructure in place)
Finally, a look at the top applications now blocked by the DCI firewall(s). The chart shows average percentage decrease in application traffic in the days before and after the election. As discussed earlier, the Iranian firewalls appear to be selectively impacting application traffic. I’ll note that ssh (a secure communication protocol) tops the list followed by video streaming and file sharing.
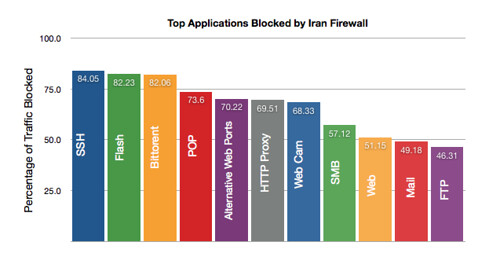
Games are not blocked. G
Thats how they are doing it, and provides a look
at couple of key targets.
A dos attack in the range of 11 to 14 Gpbs
should back up and shut down the Iranian
Internet. All of it, Government too.
But thats up the the "PersiaN Mujahideen"..
Effects of bring down Iranain Internet
Gerald
Update:
3 Iran government websites run mail servers with web interfaces
( Unconfirmed: )
webmail.bso.ir - Basij, runs Horde
mail.police.ir - Police(Obviously), squirrelmail on what appears to be a BSD box
mail.moi.ir - Ministry of Interior Exchange 6, Windows 2003
Curent Iran backbone load
.
More:
Chinese internet shut down by simple DDoS attack
Well, a large portion of it anyway. A DDoS attack on one domain server created a cascade reaction that left five provinces struggling to get online:
This is what happened during the DNSPod incident, however, it triggered a chain of unexpected events, which led to network congestions for the carrier networks. DNSPod’s servers happen to be used by Baofeng, a highly popular Chinese video streaming service. Once the millions Baofeng users fired up their desktop application, all the requests bounced off on the ISP servers, which did not know how to process them.
The intense traffic on the high-level servers caused bottlenecks, slowing everyone’s Internet connection down to a crawl. In addition to the users in the five aforementioned provinces, who were severely affected, customers in Henan, Anhui and Gansu have also reportedly experienced problems.
SOURCE:
http://www.thedarkvisitor.com/ ( temp down )
.
Labels: Iran's Blocking the Backbone, www


0 Comments:
Post a Comment
Subscribe to Post Comments [Atom]
<< Home